Your website can look completely fine on the surface and still be one misconfigured setting, one unpatched plugin, or one weak password away from a serious problem. Most operators don’t find that out until something already has.
Key Highlights
- Systematically identify potential threats to your infrastructure and data
- Evaluate your current security measures against emerging cyber threats
- Scrutinize your hosting provider for performance and security gaps
- Understand the vulnerabilities most businesses miss, from weak passwords to outdated software
- Prepare for compliance audits by documenting your risk management efforts
- Strengthen your security posture to prevent outages and data breaches
Why Website Risk Actually Matters in 2026
One security event can mean significant lost time, compromised data, and a credibility problem that follows your business for longer than you’d expect. For operators trying to grow — particularly in competitive markets like Bucks County and Montgomery County — risk management isn’t a nice-to-have. It’s part of staying operational.
What a risk assessment checklist does, at its core, is shift you from reactive to prepared. Rather than waiting for something to break, you’re moving through your setup in a structured way: reviewing your most critical assets, identifying where the weak points actually are, and thinking honestly about the threats most likely to cause trouble. That kind of preparation matters because the security landscape isn’t static. Cyber threats evolve constantly, and a checklist that worked eighteen months ago may not account for what’s circulating now. Going through this process regularly gives you a clear picture of your security posture — and a record showing you took it seriously.
What Goes Into a Real Website Risk Checklist
A solid website risk assessment checklist isn’t just a list of tasks to check off. It’s a structured process for looking honestly at your entire online setup — the obvious vulnerabilities, the less obvious ones, and the organizational habits that create gaps over time.
Good risk management practice means touching every meaningful area: potential threats, architectural weak points, hosting infrastructure, cybersecurity controls, and compliance obligations. Working through them one at a time helps surface security issues before they become incidents. So let’s start where most operators don’t — with the threats that are actually worth paying attention to.
The Threats Worth Paying Attention To
Identifying potential threats is the foundation of any risk assessment process worth running. Threats can originate inside your organization or come entirely from outside it. Either way, they’re looking for something to exploit — and when they find it, the consequences range from disrupted operations to exposed customer data. That exposure is especially costly for e-commerce businesses handling transactions.
Proactive malware scanning helps catch problems early. Threat modeling gives you a framework for anticipating where attacks are most likely to land before they actually do. Both are worth building into your regular cadence, not just your initial assessment.
Common threats to account for:
- External cyber threats — phishing, ransomware, and malware targeting your data or locking your systems
- Malicious insider actions — disgruntled employees or contractors with system access they shouldn’t have
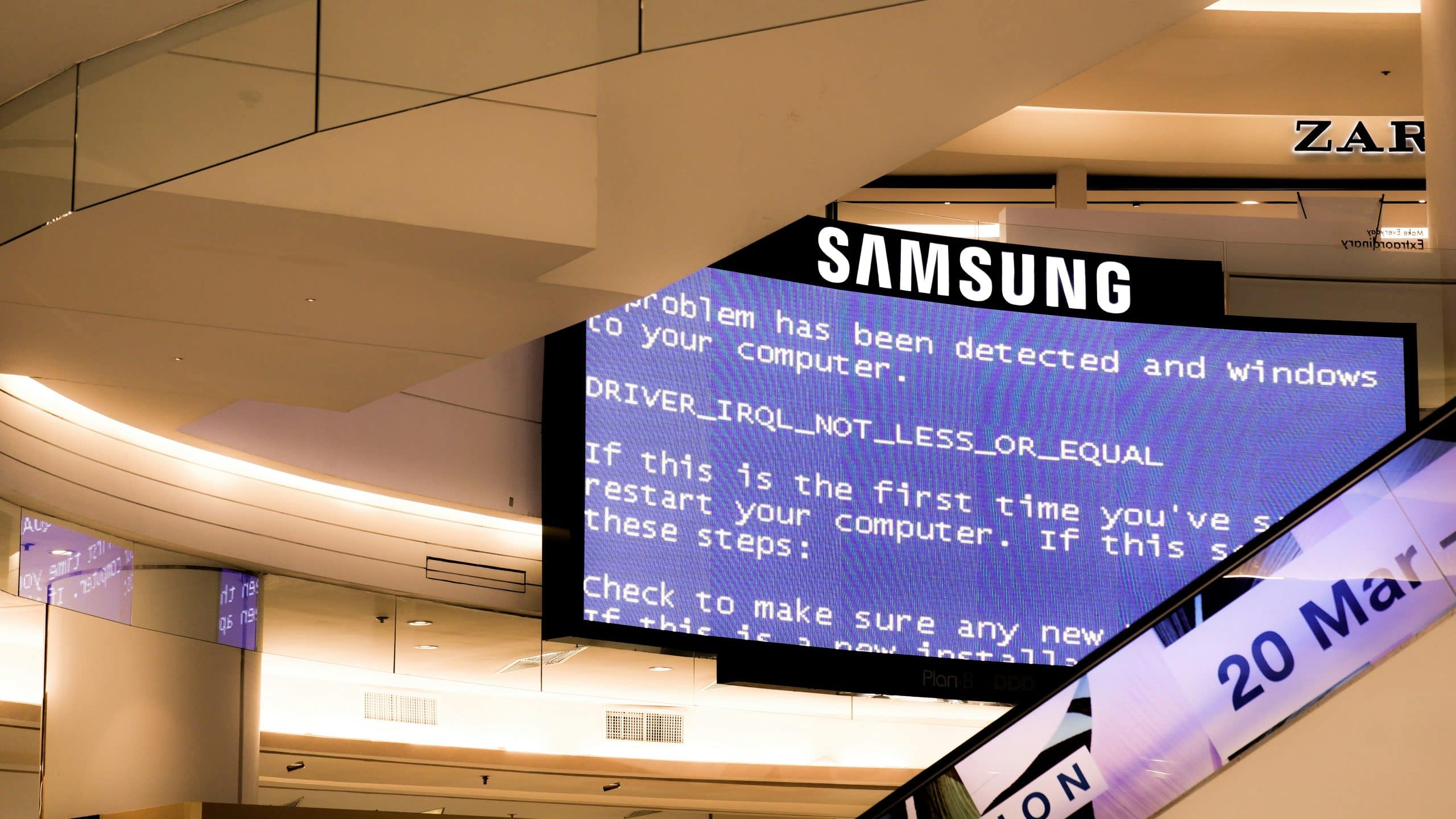
- System failures — hardware or software breakdowns that cause downtime or data loss
- Human error — honest mistakes by your team that inadvertently open the door to unauthorized access
The Vulnerabilities Most Businesses Miss
Threats come from the outside. Vulnerabilities are what they exploit on the inside. Most operators address the obvious ones and overlook the structural security gaps that don’t announce themselves — misconfigurations, over-permissioned accounts, and application vulnerabilities buried in code or workflows that haven’t been reviewed in years.
Real risk management means looking at your own systems with some skepticism. Do your access controls give users more than they need? Are default credentials still active somewhere in your stack? These aren’t exotic problems. They’re the ones that show up most consistently in post-incident reviews, because they’re easy to deprioritize until something actually goes wrong.
Vulnerabilities that tend to slip through:
- Unpatched software — running outdated applications leaves known exploits open indefinitely
- Poor access controls — excess permissions mean a compromised account has more reach than it should
- Weak passwords and credential management — easy-to-guess credentials remain one of the most common entry points
- Security misconfigurations — servers, firewalls, or cloud services set up incorrectly can expose sensitive information without any active attack needed
Your Hosting and Infrastructure Deserve a Hard Look
The hosting provider you choose and the way you’ve structured your hosting infrastructure have more to do with your site’s security and reliability than most operators realize. These decisions affect your ability to absorb attacks, maintain uptime, and recover when something goes wrong. That’s why hosting belongs in your asset inventory, not at the bottom of your checklist.
Hosting cost isn’t just a line item — it reflects the level of security, performance, and support you’re actually getting. Under-resourced hosting shows up as more frequent downtime and a weaker security posture, and the cost of those outcomes typically exceeds the monthly fee difference many times over. Here’s how to evaluate it properly.
What to Actually Evaluate When Comparing Hosting Providers
Vendor evaluation for hosting should go well past marketing pages and pricing tiers. The right provider offers defensible security measures, a clear uptime commitment, and support that’s actually reachable when something breaks. Documenting your evaluation process makes the decision defensible and gives you a reference point when it’s time to reassess.
Your review should cover technical specifications, security protocols, and service level agreements. For businesses in Horsham, Doylestown, or anywhere operating with lean IT resources, local performance and support responsiveness are legitimate factors.
| Feature | What to Look For |
| Security Measures | Firewalls, DDoS protection, malware scanning, intrusion detection systems |
| Uptime Guarantee | A clearly defined SLA (e.g., 99.9% uptime) with stated compensation for failures |
| Backup Solutions | Automated daily backups, easy restoration process, offsite storage options |
| Support | 24/7 availability, multiple contact channels, demonstrable expertise |
| Compliance | Adherence to PCI DSS, HIPAA, or GDPR where applicable |
Uptime Isn’t Guaranteed — Here’s How to Protect It
Even a reliable hosting provider can’t promise zero downtime. Hardware fails. Software has bugs. Attacks happen. The goal isn’t eliminating that risk — it’s reducing exposure and responding fast when something goes sideways.
Uptime monitoring tools check your site from multiple locations and alert you the moment something looks wrong. Intrusion detection systems watch network traffic in real time, flagging suspicious activity before it escalates. Regular audits on your server configuration catch misconfigurations and resource issues before they become outages.
To protect availability, work through these:
- Implement proactive uptime monitoring — use a third-party tool to check from multiple locations continuously
- Deploy intrusion detection systems — monitor network traffic for patterns that suggest an incoming attack
- Establish a failover system — have a backup environment that can take over if the primary goes down
- Conduct regular audits — review server settings and resource usage periodically to catch problems before they surface publicly

Backups and Recovery: The Part Nobody Thinks About Until It’s Too Late
A strong backup and recovery plan is arguably your most underrated risk mitigation tool. Whether the cause is a cyberattack, accidental deletion, or hardware failure, the ability to restore your site quickly is what separates a recoverable incident from a serious one.
The mistake most businesses make is treating backups as someone else’s responsibility — assuming the hosting provider handles it, or setting up automated backups once and never verifying they actually work. Neither approach holds up when something goes wrong.
Add these to your risk assessment checklist:
- Automate and verify backups — daily automated backups are the baseline; periodic restoration tests confirm they’re actually usable
- Use offsite storage — a copy stored in a separate environment or in the cloud survives scenarios that would take down your primary setup
- Document the recovery process — written, step-by-step recovery instructions mean anyone on your team can execute them under pressure
Cybersecurity Basics That Still Get Skipped
More sophisticated threats get the attention, but a surprising number of security problems trace back to basics that were never implemented or gradually fell out of maintenance. A thorough risk analysis surfaces these consistently — missing security controls, outdated software, weak credentials sitting in systems nobody’s reviewed lately.
Application security fundamentals aren’t just for enterprise organizations. They apply to any business operating online, and the gap between businesses that have them and businesses that don’t is significant. Here’s where to focus.
The Security Controls Every Site Should Have in Place
Security controls are your first line of defense. SSL certificates protect data in transit. Access controls limit the blast radius if credentials are compromised. A web application firewall filters out malicious traffic before it reaches your application. Multi-factor authentication adds a layer that stops a large percentage of credential-based attacks outright.
Each of these is a distinct protection. None of them substitute for the others.
Every site should have:
- Strict access controls — minimum necessary permissions, nothing more
- SSL certificates — encrypting data in transit is non-negotiable in 2026
- Strong passwords and MFA — enforce both, not one or the other
- Web Application Firewall (WAF) — filter malicious traffic at the perimeter
How User Data Gets Exposed and How to Close That Gap
Data breaches rarely happen because of one sophisticated attack. More often, they’re the result of accumulated gaps in security policies — weak passwords, unpatched software, over-permissioned user roles, and unclear procedures for handling sensitive information.
Closing those gaps starts with written, enforced policies. Who has access to customer data? How is that data stored and transmitted? What happens when a potential breach is detected? These aren’t abstract questions — they’re the foundation of a practical security plan that holds up under scrutiny.
Common exposure points and how to address them:
- SQL injection — weak web form validation lets attackers query your database directly; parameterized queries prevent this
- Unencrypted data — sensitive information stored or transmitted in plain text is easy to intercept; encrypt both at rest and in transit
- Leaked credentials — weak or reused passwords remain a primary attack vector; strong password policies combined with MFA raise the bar substantially
- Exposed APIs — third-party integrations without proper authentication controls create access points that are easy to miss in a standard review
Accessibility and Compliance Aren’t an Afterthought
In 2026, accessibility and regulatory compliance are risk categories with real financial and legal consequences attached to them. ADA compliance for websites isn’t optional — lawsuits related to web accessibility have increased steadily, and they aren’t limited to large companies. Privacy risk and industry-specific regulations carry their own penalties, and ignoring them doesn’t make the obligation go away.
Your risk assessment needs to include a compliance layer. Regular compliance audits help protect the business and demonstrate that you’re operating with appropriate standards in mind.

What Federal, State, and Industry Requirements Actually Apply to You
The regulations that apply to your business depend on what you do and what kind of data you handle. E-commerce sites need to account for PCI DSS. Any business collecting or processing health information is subject to HIPAA. If you’re collecting data from EU residents, GDPR applies regardless of where your business is located. Pennsylvania businesses also have state-level privacy obligations worth understanding alongside federal requirements.
Key regulations to know:
- PCI DSS — required for any business accepting or handling credit card data
- HIPAA — applies to businesses handling protected health information
- GDPR — relevant if you collect data from EU residents in any capacity
Building a Paper Trail That Holds Up
Good documentation is how you demonstrate, under pressure, that your security posture is intentional and maintained — not assembled after the fact. If an audit happens or an incident occurs, your records are what determine whether your response looks credible.
Documentation isn’t a one-time exercise. Your security plan, your risk assessment reports, your vendor evaluation records — all of these need to reflect your current setup, not the one you had two years ago. That living record is what compliance audits are looking for.
Your documentation should include:
- A formal security plan — written security policies, procedures, and controls
- Risk assessment reports — findings and remediation steps from each audit cycle
- Vendor evaluation records — documentation of your hosting provider and key third-party integrations review
- Incident response plans — step-by-step actions for likely scenarios, documented before you need them
Keeping the Checklist Working After You Build It
Building a website audit checklist is the right first step. Keeping it current is the actual work. Your security environment changes. Your business changes. New integrations get added. Team members turn over. Regulations evolve. A checklist that isn’t revisited starts reflecting a reality that no longer exists, and that gap is where risk accumulates quietly.
Set a review schedule and treat it like any other operational obligation — not something that waits for an incident to prompt it. At Mutewind Digital, this kind of ongoing infrastructure review is part of how we approach long-term partnerships, not a one-time deliverable.
When to Bring in Outside Eyes
Operator self-assessment has real limits. Familiarity with your own setup creates blind spots, and internal teams often don’t catch what they’ve stopped noticing. A third-party security audit brings a fresh perspective and a different set of questions — and outside reviewers consistently find vulnerabilities that internal reviews miss.
Vulnerability scans and penetration tests go further by simulating real attack conditions. Rather than asking whether a defense looks correct on paper, they test whether it holds up in practice. That’s a meaningful distinction, and one that’s worth making before something more consequential tests it for you.
Consider an outside audit in these situations:
- Annually — as a standing practice, not just when something feels off
- After a security incident — to understand what happened and close the underlying gap
- Before launching a new application — to catch problems in new code before they’re exposed publicly
Want an outside look at your site’s actual risk level? Reach out to Mutewind Digital to schedule an audit conversation.
Frequently Asked Questions
What are the most common website vulnerabilities operators overlook?
Outdated plugins, misconfigured access controls, and weak password policies come up most consistently. These application vulnerabilities don’t always look dangerous until they’re exploited. Each one creates an opening that can compromise the entire site’s security posture without any sophisticated attack required.
How can infrastructure decisions impact security and costs?
Your hosting infrastructure directly shapes your security baseline and your long-term exposure. Providers that underinvest in security measures create gaps that cost far more to address after an incident than a better hosting arrangement would have cost upfront. Regular audits of your setup help make sure you’re getting the protection your risk profile actually requires.
How often should a website risk checklist be revisited?
At minimum, once a year — and also following any significant changes to your site, application stack, or team structure. Consistent regular audits keep your risk assessment current and make sure new security gaps don’t go unnoticed between formal reviews.
